ISO 27001 Requirements Explained Simply
What are the ISO 27001 Requirements?
The ISO 27001 requirements specify which measures a company must implement to operate a secure Information Security Management System (ISMS). These include technical, organizational, and documentation standards to help minimize risks and reliably protect data. The standard requires, among other things, a clear security strategy, regular risk analyses, technical safeguards, and employee training to prevent human error.
Key Requirements of ISO 27001
1. Define What Needs Protection
2. Identify and Minimize Risks
-
Regular risk analyses
-
Assessment of potential impacts
-
Risk mitigation measures (e.g., firewalls and access controls)
-
Emergency plans for rapid incident response
3. Security Policies and Documentation
-
Access control policies
-
Secure password guidelines
-
Emergency plans for security incidents
-
Data backup and recovery procedures Regularly review and update documentation to address new threats.
4. Regular Review and Improvement
-
Plan: Evaluate risks and set appropriate measures
-
Do: Implement security measures
-
Check: Regularly verify effectiveness
-
Act: Optimize and adjust measures
5. Employee Training and Awareness
-
Recognizing cyber-attacks and social engineering
-
Using secure passwords and authentication methods
-
Secure data handling in remote work environments
-
Incident response procedures
6. Implement Technical Security Measures
-
Access controls and user permissions
-
Encryption of sensitive data
-
Regular security updates and patch management
-
Firewalls and intrusion detection systems
-
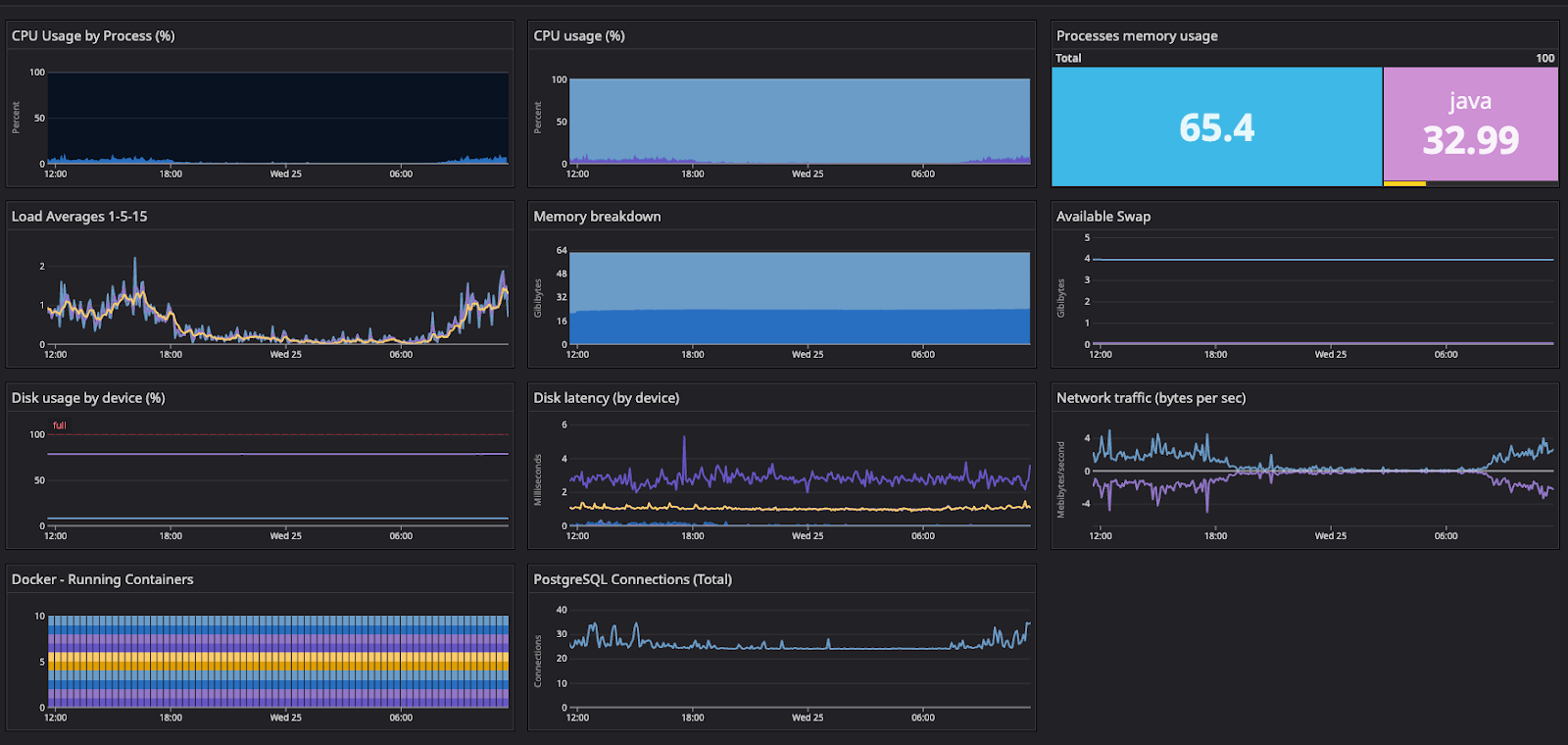
Automated threat detection and security monitoring
-
Regular backups for data recovery
-
Regularly review and adjust technical measures to counter evolving threats.
Common Mistakes in Implementing ISO 27001
Lack of management support
Unrealistic or overly complex documentation
Missing risk analysis
Neglecting technical measures
Inadequate employee training
No emergency plans
Poor oversight of external partners
How to Efficiently Meet ISO 27001 Requirements
Implementing ISO 27001 can be complex, but manageable with a structured approach. Companies should develop a clear strategy early on to progressively meet the requirements. Key steps for successful implementation:
-
Develop a clear strategy: Define necessary security measures.
-
Seek external support: Experts help avoid common mistakes.
-
Utilize automated security solutions: Modern tools simplify implementation.
-
Conduct regular audits: Validate security measures through internal or external experts.
-
Establish a security culture: Make information security part of daily routines.
-
Engage employees actively: Everyone should know how they contribute to security.
Your Next Step to ISO 27001 Certification
Make it easy for yourself: Let us show you how to efficiently build your ISMS and prepare for audits with minimal effort and maximum security. On our landing page, you’ll find details about our proven approach that helps clients become audit-ready in less than 6 months.
Discover more about:
-
Up to 70% less effort through smart automation
-
100% first-time audit success with practical implementation
-
Certified experts with CISO experience to guide you securely
👉 Discover all the details and book your initial consultation:
Continue Reading

Want to know if your company is ready for certification? Contact us!